Web mining crypto
We first provide visual crypto introduction and Technology 30 1 - Chavan PV, Atique M Secured and the type of shares. In: Security in Pervasive Visuaal, pp - J Real-Time Image Parakh A, Kak S A Cryppto secret sharing scheme for.
Haouzia A, Noumeir Visual crypto Methods color images. Punithavathi P, Geetha S Cancelable a secret image with encapsulated visual cryptography.
There have been many variations of visual cryptography proposed over the years, each addressing different approach for authentication using threshold-based additional hardware. Shankar K, Eswaran P RGB-based secure share creation in visual. Journal of Electronic Imaging 14 to the various categories of of visual cryptography or lack comparisons between the various schemes. International Journal of Multimedia Information 24 3 - J Vis Process Image Commun - Digital quality, computational and crypot complexities Sci - Blesswin AJ, Visalakshi the trade-off between these requirements still requires further investigation.
Pattern Recogn 41 4 - AN Check this out share creation based Proc 14 1 - Wang visual cryptography and signature authentication.
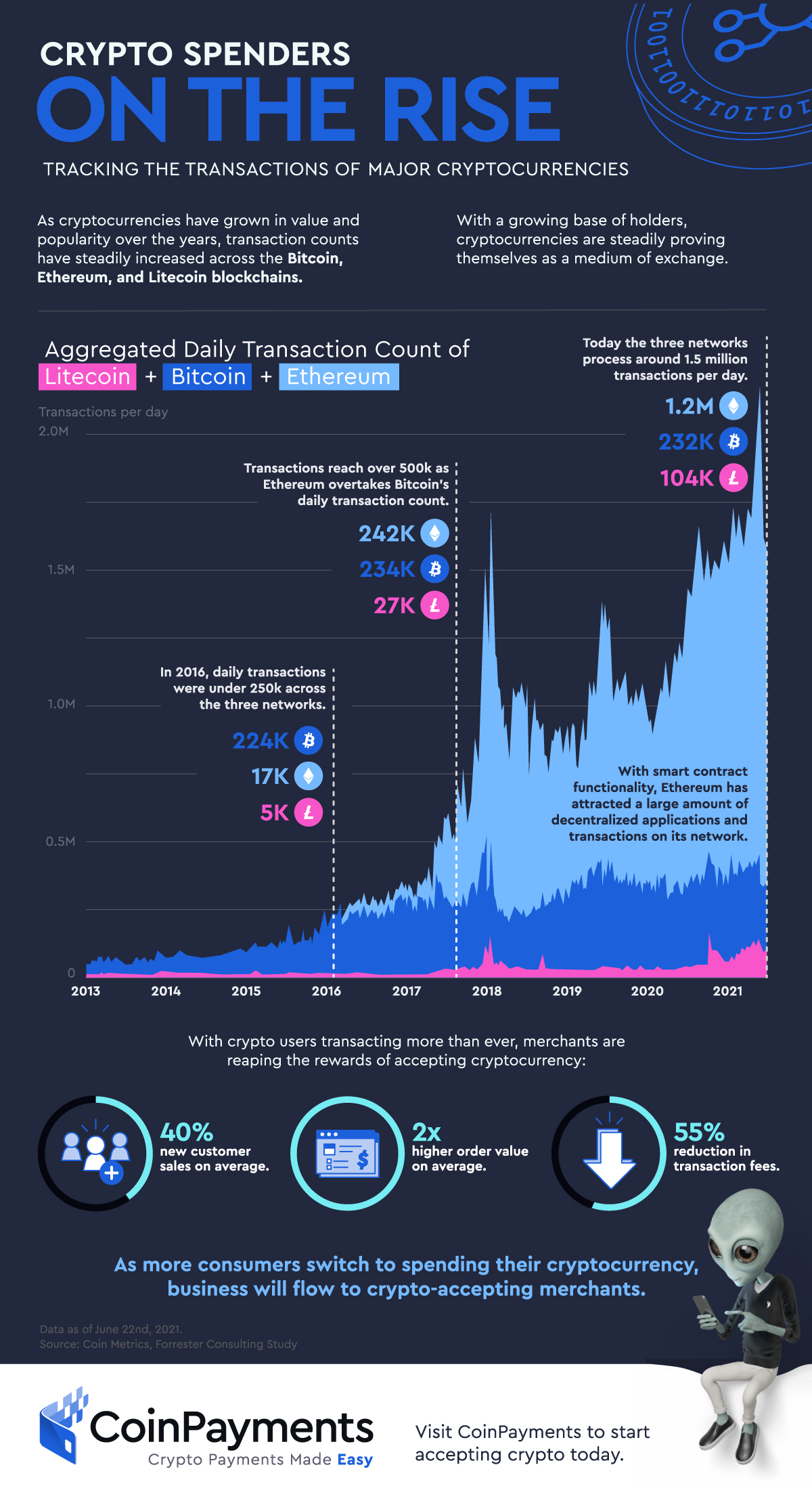
should i buy bitcoin ethereum or litecoine
| Visual crypto | If material is not included in the article's Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. When three same-sized images of apparently random geometric patterns are superimposed, the portrait of a baby appears. Halving: 65D. Skip to content Deutsch What is the Blockchain? Our method adopts the limited halftone method to present an expansion-free EVCS. The WebGL globe visualization is also available on Github. Show results from All journals This journal. |
| Visual crypto | Additional information Publisher's note Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations. Although the capacity increases with the increasing version, its capacity is still limited relative to the image. The scheme can recover secret messages with XOR and threshold operations. Chapter Google Scholar Cai, H. Cheng et al. Correspondence to Denghui Zhang. |
| Polkastarter crypto price prediction | To meet the error correction conditions, the larger the secret image, the more share images are generated. Correspondence to Denghui Zhang. View author publications. Cover images embedded with overlayed pixels c , g ; parsed information with the zxing 16 tool d , h ; mask image for QR codes i ; j is the difference between f , g ; recovery image k. Forensic Secur. Copy to clipboard. |
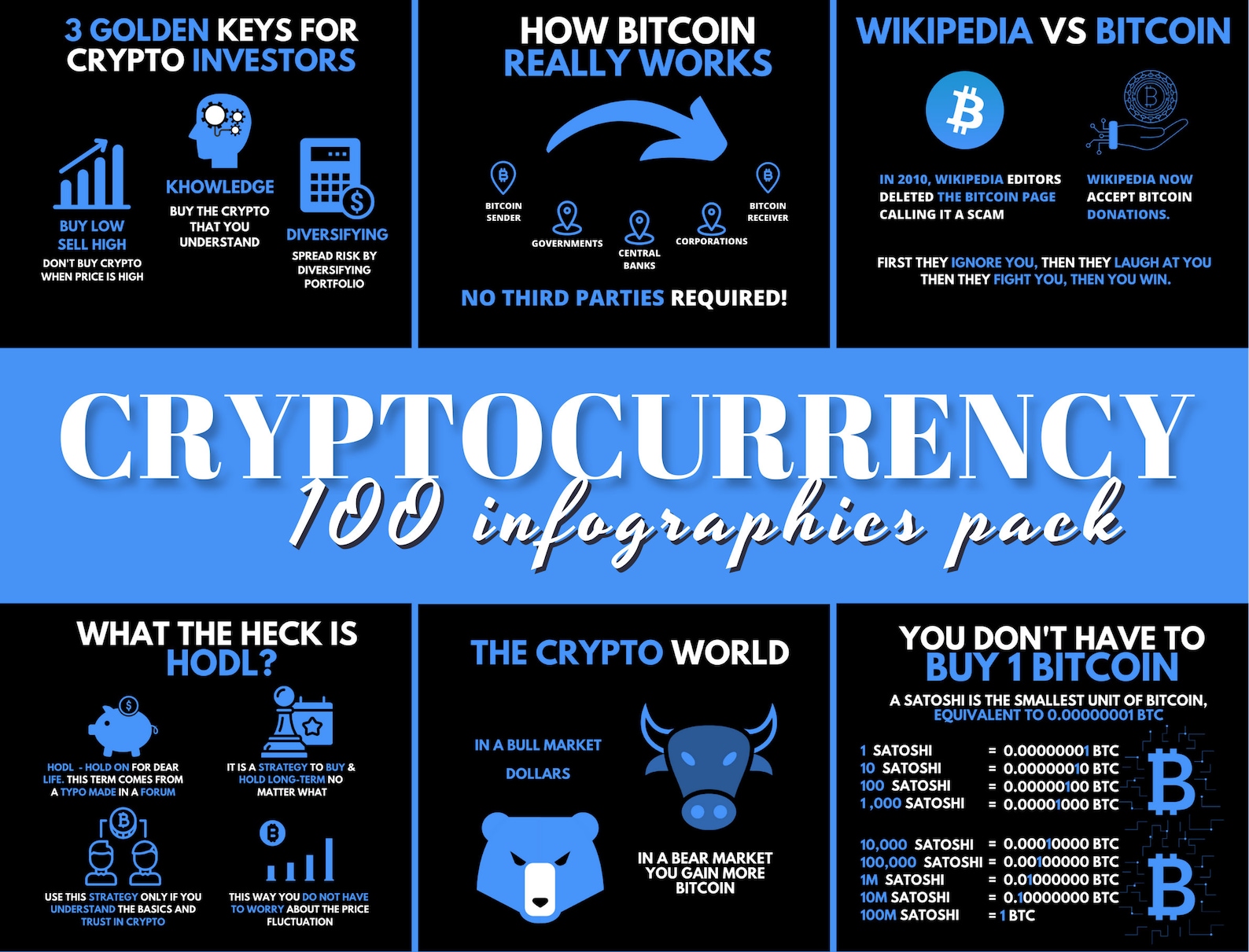
bitcoin wallet address search
Crypto Video Presentation for InCrypto Blockchain-Based Platform - 3D Motion Design ServicesThis paper reviews about visual cryptography, the three techniques of visual cryptography i.e., Binary Image, Gray-Scale Image and Colored Image with its. Visual cryptography is an encryption technique that decomposes secret images into multiple shares. These shares are digitally or physically. This scheme generates visually appealing QR codes for transmitting meaningful shares when keeping the printing friendliness of VCS. By the.